EXAMPLEDESCRIPTION
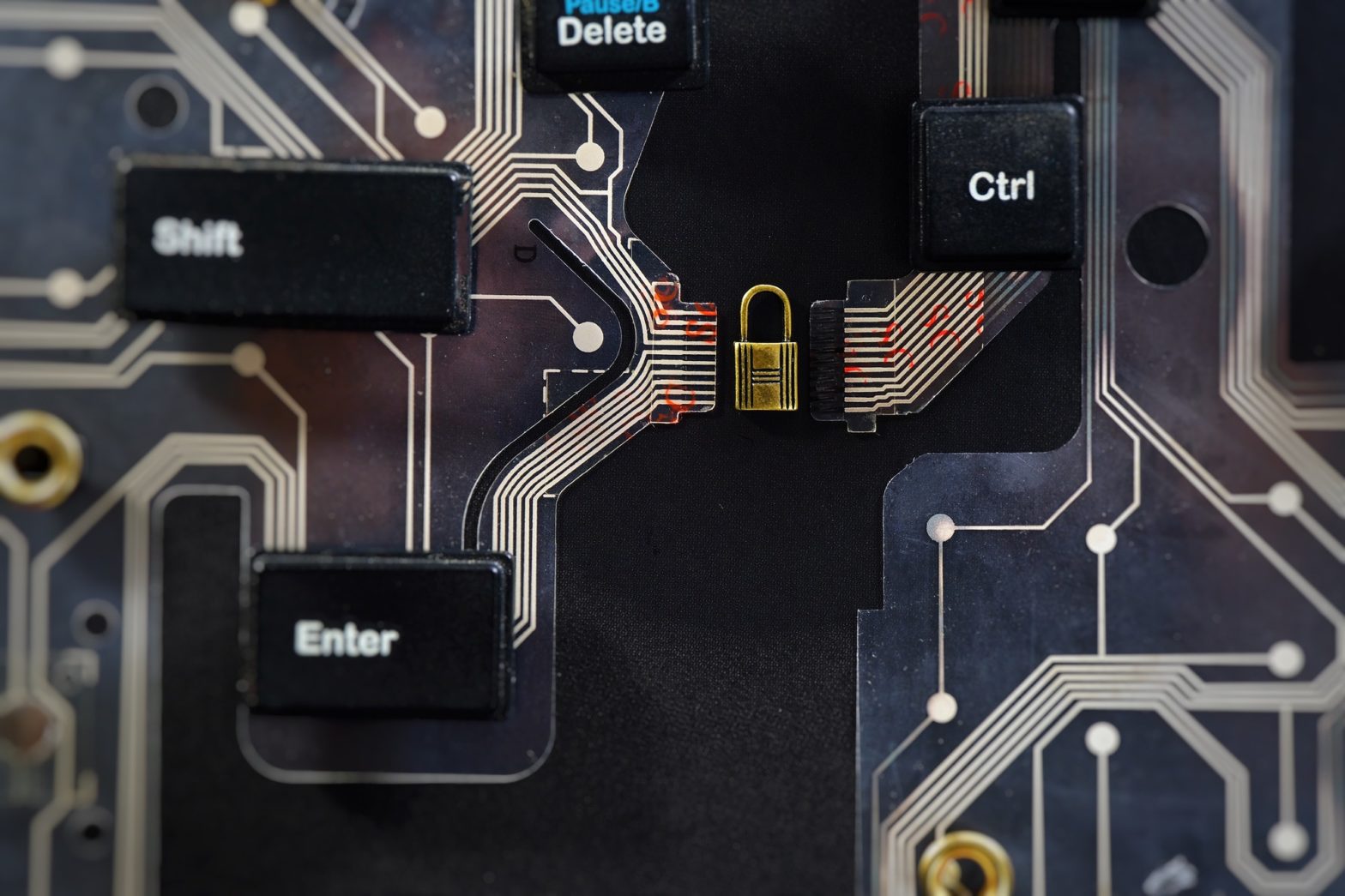
Iron Range Cyber Named as One of the Leading Cybersecurity Companies on Manifest

At Iron Range Cyber, we empower our clients through their digitalization efforts by providing them with robust and secure cyber systems. Our mission is to help SMEs combat risks in their cyber security through comprehensive cyber protection solutions. Today, we’re excited to report that we’ve been named as one of the leading companies on The… Continue reading Iron Range Cyber Named as One of the Leading Cybersecurity Companies on Manifest